
1introjunos
.pdf
Introduction to JUNOS Software
|
|
Reproduction |
|
Simple Network Management Protocol |
|
|
The slide highlights the topic we discuss next. |
|
Not |
for |
|
|
|
|
Secondary System Configuration • Chapter 5–33
Introduction to JUNOS Software
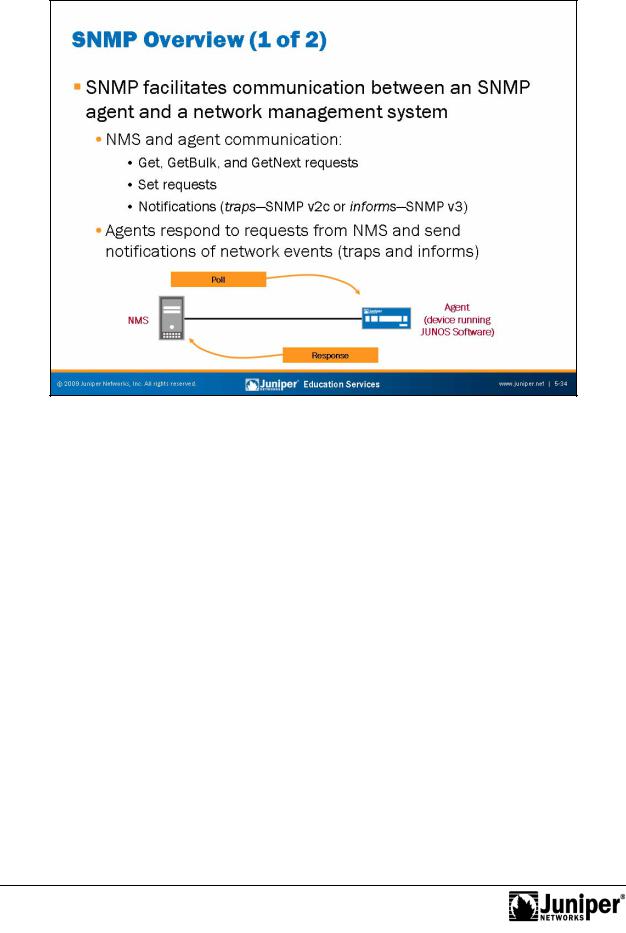
Devices running JUNOSReproductionSoftware act as SNMP agents. An SNMP agent exchanges network management information with SNMP manager software running on a network
managementforsystem (NMS) or host. The agen responds to requests for information and actions m the manager. An agent communicates with the SNMP manager using the ll wing message types:
Get, Getbulk, or Getnext requests: The SNMP manager requests information from an SNMP agent. The agent responds with a Get response message;
Set requests: The SNMP manager changes the value of a Management Information Base (MIB) object controlled by the agent. The agent returns the status in a Set response message; and
Notifications: The SNMP agent sends traps to notify the manager of significant events regarding the network device. SNMP version 3 uses informs to notify the manager of significant events. Informs increase SNMP reliability by requiring the receiver to acknowledge the receipt of an inform notification.
By polling managed network devices, the NMS collects information about network resources. An SNMP agent can also notify the NMS of events and resource constraints through the use of SNMP traps.
Chapter 5–34 • Secondary System Configuration
Introduction to JUNOS Software
ManagementReproductionInformation Bases
A MIB is a collection of objects maintained by the SNMP agent in a hierarchical fashion. The SNMP manager views or changes objects within the MIB structure. MIBs canforbe defined at the enterprise level to provide enterprise-specific information about the managed network device, or MIBs can be standardized to provide common
in rmati n across multiple vendor network devices. NMS devices poll object
identi iers (OIDs) to retrieve management information. An OID is considered a leaf in Nothe tree-like hierarchy of a MIB. The Internet Engineering Task Force (IETF) provides
s andard MIBs you can download at http://www.ietf.org. You can download Juniper Networks enterprise MIBs at http://www.juniper.net/techpubs.
JUNOS Software SNMP Support
JUNOS Software provides support for SNMP versions 1, 2c, and 3. Version 1 is the initial implementation of SNMP that defines the architecture and framework for SNMP. Version 2 added support for community strings, which act as passwords determining access to SNMP agent MIBs. SNMPv3 is the most up-to-date version and provides enhanced security features including the definition of a user-based security model (USM) and a view-based access control model (VACM). SNMPv3 provides message integrity, authentication, and encryption, and is a superior security model over SNMPv2c, which uses plain text community strings. JUNOS Software also provides support for remote monitoring (RMON) events, alarms, and history.
Secondary System Configuration • Chapter 5–35
Introduction to JUNOS Software
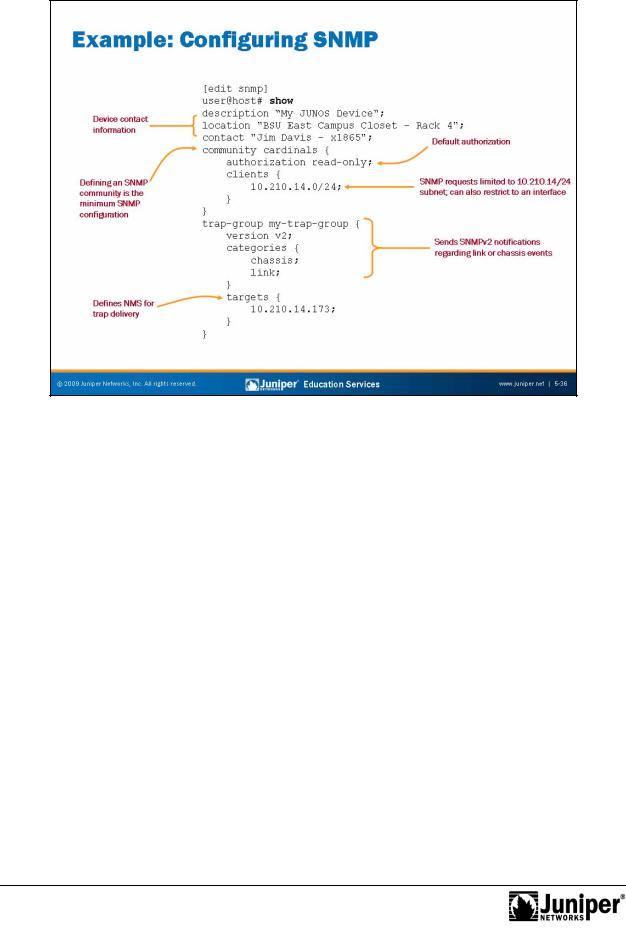
Sample SNMP ConfigurationReproduction
The slide shows a sample SNMP configuration using some common SNMP
configuration options. When configuring contact information, you must be as specific as possiblefor. This info mation is useful when trying to resolve issues with a network
device. The example estricts SNMP access to the 10.210.14.0/24 network with
read-only auth rizati n. The example also shows the configuration of an SNMP trap
group, necessary r the delivery of SNMP traps to an NMS. Not
Chapter 5–36 • Secondary System Configuration

Introduction to JUNOS Software
Monitoring SNMP Op ration
|
An NMS or host provides the interface for most SNMP monitoring. To monitor SNMP |
|
operation di ectly from a device running JUNOS Software, you can use traceoptions, |
|
system logging, and various show snmp commands. When a trap condition occurs, |
|
s me t aps a Reproductionlogged if the system logging is configured with the appropriate facility |
|
and severity levels, regardless of whether a trap group is configured. The sample |
Not |
sh w c mmand output on the slide illustrates that you can also issue standard SNMP |
formanager commands to view agent OID values. You can specify the OIDs in ASCII text |
|
f rmat or dotted-decimal notation.
Secondary System Configuration • Chapter 5–37
Introduction to JUNOS Software
This Chapter Discuss d:
• |
User authentication methods and configuration; |
• |
Configu ing and analyzing system logging and tracing; |
• |
NTP c nfigurationReproductionand operation; |
• |
Archiving configurations on remote devices; and |
•forConfiguring and monitoring SNMP. |
|
Not |
|
Chapter 5–38 • Secondary System Configuration
Introduction to JUNOS Software
Not
2. |
Reproduction |
Review Questions |
|
1. |
|
for |
|
3. |
|
4. |
|
Secondary System Configuration • Chapter 5–39
Introduction to JUNOS Software
|
|
Reproduction |
Lab 3: Secondary Syst m Configuration |
||
The slide provides the objective for this lab. |
||
Not |
for |
|
|
|
|
Chapter 5–40 • Secondary System Configuration

Introduction to JUNOS Software
Chapter 6: Operational Monitoring and |
||
|
|
Reproduction |
Maintenance |
||
Not |
for |
|
|
|
|

Introduction to JUNOS Software
This Chapter DiscussReproductions:
• Monitoring platform and interface operations;
•forNetwo k utilities and usage guidelines;
• Maintaining JUNOS Software; and
• Per rming password recovery. Not
Chapter 6–2 • Operational Monitoring and Maintenance
