
Advanced Wireless Networks - 4G Technologies
.pdf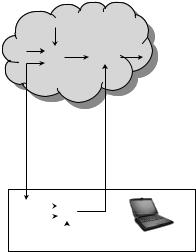
608 SECURITY
Fixed network
|
|
IMSI |
|
K |
|
SRESS |
Yes/No |
|
i |
/No |
|
Ri |
A3 |
Compare |
|
|
|
||
Radio |
|
path |
SRES |
|
|
|
A3 |
|
|
|
Ki |
|
|
|
Response |
||
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
|
|
Mobile |
|
|
|
|
IMSI |
|||
Figure 15.9 Generic authentication process.
both at the MS (mobile station) and at the AuC, a signed response (SRES), using an individual secret key Ki attached to the mobile subscriber. The number RAND, whose value is drawn randomly between 0 and 2128 − 1, is used to generate the response by the mobile as well as by the fixed part of the network. The authentication process is carried out both at the mobile and at the MSC simultaneously. The BSS remains transparent to this process. The mobile only receives the random number over the radio path and in turn returns the signed response to the network. Thus, an air interface mobile designation is not disclosed. At subscription time, the subscriber authentication key Ki is allocated to the subscriber together with its IMSI (international mobile station identity). The key Ki is stored in the AuC and used to generate a triplet (Kc, signed response, RAND) within the GSM system. As stated above, the same Ki is also stored at the mobile in the subscriber ID (SIM). In the AuC, the following steps are carried out in order to produce one triplet. A nonpredictable RAND is produced. RAND and Ki are used to calculate the signed response and the ciphering key (Kc) using two different algorithms (A3, A8). This triplet (RAND, signed response, and Kc) is generated for each and every user and is then delivered to the HLR. This procedure is shown in Figure 15.10 [41–43].
The AuC begins the authentication and cipher key generation procedures after receiving an identification of the subscriber from the MSC/VLR. The AuC first queries the HLR for the subscriber’s authentication key Ki . It then generates a 128 b RAND for use as a challenge (nonce), to be sent to the MS for verification of the MS’s authenticity. RAND is also used by the AuC, with Ki in the algorithm A3 for authentication, to calculate the expected correct signed response from the MS. RAND and Ki are also used in the AuC to calculate the cipher key Kc with algorithm A8. The signed response is a 32 b number, and Kc is a 64 b number.
The values of RAND, signed response and Kc are transmitted to the MSC/VLR for interaction with the MS. Algorithms A3 and A8 are not fully standardized by GSM and

SECURITY MANAGEMENT IN GSM NETWORKS |
609 |
|
|
|
Triplet |
|
|
|
RAND |
|
|
|
|
|
|
SRES |
|
|
|
|
|
|
Kc |
|
|
|
|
|
|
AUC |
Kc |
|
|
|
|
(Kc, SRES |
|
64 b |
SRES |
32 b |
RAND |
and RAND |
|
|
|
|
|
|
|
generation) |
|
Algorithm for |
Algorithm for |
|
|
||
|
ciphering |
|
authentication |
|
|
|
|
A8 |
|
A3 |
|
|
|
|
Database: |
|
Generation |
|
||
IMSI and authentication |
|
of random |
|
|
||
|
|
Kn |
|
numbers |
|
|
K1 |
K22 |
|
|
|
|
|
|
|
|
|
|
RAND |
|
IMSI 1 |
IMSI 2 |
IIMSI n |
|
|
|
|
IMSI: international mobile subscriber identity
Kc: ciphering key
Kn: subscriper authentication key
SRES: signed response
RAND: random number
Figure 15.10 Generation of Kc, signed response, and RAND at the AuC.
may be specified at the direction of PLMN operators. Different PLMNs may use different and proprietary versions of these algorithms. Also, to protect the secrecy of the user, the authentication key Ki is not sent to the MSC/VLR. Based on the discretion of the PLMN operator, Ki can be of any format and length. The MSC/VLR forwards the value of the RAND to the MS, which also has the correct Ki and algorithm A3, which is stored in its SIM. The SIM then uses RAND and Kc in these algorithms to calculate the authentication SRESc and the cipher key, Kc. The MS sends the calculated response, SRESc, back to the MSC/VLR, which compares it with the value signed response received from the HLR/AuC. If the SRESc and the signed response agree, the subscriber access to the system is granted, and the cipher key Kc is transferred to the BTS for use in encrypting and decrypting messages to and from the MS. If the SRESc (computed signed response at the mobile) and the signed response disagree, the subscriber access to the system is denied. In summary, the VLR initiates authentication toward the MS and checks the authentication result. The complete process is shown in Figure 15.11.
The ciphering/deciphering algorithm (called A5) uses a cipher key Kc, which is allocated to each mobile subscriber during the authentication procedures. The key Kc is computed from the RAND by an algorithm (called A8) driven by the mobile subscriber authentication key Ki . Algorithm A8 is common to all GSMs. Figure 15.10 has shown the process of generating Kc. For the authentication procedure, when a signed response is being calculated at the mobile, the ciphering key (Kc) is also calculated using another algorithm (A8), as shown in Figure 15.11. This key is set in the fixed system and in the MS. At the ciphering

610 SECURITY
Key |
SIM |
|
|
pad |
card |
|
Store |
|
K1 |
A8 |
|
|
K |
||
|
|
|
c |
|
A3 |
|
|
Mobile |
|
|
|
RAND |
SRESC |
Send to BTS |
(128 b) |
(32 b) |
|
|
Deny |
|
|
|
|
|
|
access |
|
|
|
|
|
MSC/ |
|
? |
|
|
Transfer |
|
VLR |
No |
SRES= |
Yes |
Access |
||
cipher key |
||||||
|
|
SRESC |
|
granted |
||
|
|
|
to BTS |
|||
|
RAND |
SRES |
|
Kc |
||
|
|
(cipher key |
||||
|
(128 b) |
(32 b) |
|
|||
|
|
64 b) |
||||
|
|
|
|
|
||
HLR, home location register
Figure 15.11 Authentication process in GSM system.
start command (from VLR to BSS), Kc is used by the MS and the BTS in order to cipher and decipher the bitstream that is sent over the radio path. In addition to the authentication procedures, a key setting may be initiated by the network as often as the network operator wishes. The command to use the encryption key is sent over the logical channel and dedicated control channel, as soon as the identity of the mobile subscriber is known by the network.
The key Kc must be agreed upon by the mobile station and the network prior to the start of encryption. The choice in GSM is to compute the key Kc independently from the effective start of encryption during the authentication process. Kc is then stored in a nonvolatile memory inside the SIM so as to be remembered even after a switched-off phase. This key is also stored in the visited MSC/VLR on the network side and is ready to be used for the start of encryption. The actual encryption/decryption of user data takes place within the mobile station and the BSS. For this purpose, the encryption key is downloaded from the MSC to the BTS via the BSC. After authentication, the transmission is ciphered, and Kc is used for ciphering/deciphering. This process is shown in Figure 15.12. Data flow on the radio path is obtained by a bit-per-bit binary addition of the user data flow and ciphering bitstream generated by the GSM algorithm A5 using a ciphering key (Kc). This exact process of encryption/decryption at the mobile and at BTS is shown in Figure 15.13. Code words S1 and S2 for downlinks and uplinks are changed at every frame. When modulo 2 is added with plain text, S1 outputs cipher text. On the other side, the cipher text, when modulo 2 is added with S1, outputs the plain text. The ciphering/deciphering function is placed on the transmission chain between the interleaver and the modulator. Since A3 and A8 are always running together, these two are implemented as a single algorithm in most cases. The algorithm A3 is standardized in the whole of GSM.


612 SECURITY
15.5 SECURITY MANAGEMENT IN UMTS
Cryptographic functions used in UMTS are specified below:
Algorithm: Purpose/usage
O,S (operator specific, fully standardized)/location in the network
f0 : random challenge generating function O /AuC
f1 : network authentication function O – (MILENAGE) /USIM and AuC
f1* : resynchronization message authentication function O – (MILENAGE) /USIM and AuC
f2 : user challenge-response authentication function O – (MILENAGE) /USIM and AuC
f3 : cipher key derivation function O – (MILENAGE) /USIM and AuC f4 : integrity key derivation function O – (MILENAGE) /USIM and AuC
f5 : anonymity key derivation function for normal operation O – (MILENAGE) /USIM and AuC
f5* : anonymity key derivation function for resynchronization O – (MILENAGE) /USIM and AuC
f6 : MAP encryption algorithm S/MAP nodes
f7 : MAP integrity algorithm S/MAP nodes
f8 : UMTS encryption algorithm S – (KASUMI)/ MS and RNC
f9 : UMTS integrity algorithm S – (KASUMI) / MS and RNC

614 SECURITY
covers both the MAPsec specification and specifications for how to protect IP connections on the control plane of the UMTS core network [51].
The second AKA stage is where the SGSN/ VLR executes the one-pass challengeresponse procedure to achieve mutual entity authentication between the USIM and the network (SN, HE). A point to be made is that, in a two-staged AKA approach, the HE delegates responsibility for executing the security procedures to the SN. There must therefore be a trust relationship between the HE and the SN in this matter. In the GSM environment, this trust relationship is regulated through roaming agreements; the same model should be applicable to UMTS. The cryptographic functions ( f 0 − f 5*) used in the AKA procedure are implemented exclusively in the USIM and AuC. UMTS operators are free to choose any algorithm they want provided it complies with the function input/output specification given in Reference [49]. However, 3GPP has developed the MILENAGE [51, 52] algorithm set to provide the AKA functions. The formal status of MILENAGE is that it is provided as an example algorithm set, but in practice it is the recommended algorithm set for the AKA functions.
MILENAGE itself is built around the symmetric block cipher Rijndael. A consequence of having mutual authentication is that the USIM is now an active entity. In GSM, the user could not authenticate the network; hence, the UE could not reject the network. In UMTS, the USIM will attempt to authenticate the network and it is now possible that the USIM will reject the network. Details on the implementation of different security services in UMTS can be found in References [46–60].
15.6 SECURITY ARCHITECTURE FOR UMTS/WLAN INTERWORKING
As specified in Chapter 1, 4G will integrate different wireless systems and provide intertechnology roaming. Security architectures will depend on the type (tight or loose) of interworking. A tight UMTS/WLAN interworking solution would mandate the full 3GPP security architecture and require the 3GPP protocol stacks and interfaces to be present in the WLAN system [64] . The loose interworking options merely require the 3GPP authentication method to be implemented. To avoid link layer modifications, the authentication protocol is allowed to run at the link layer using Internet protocols – extensible authentication protocol (EAP) [63] and authentication, authorization and accounting (AAA) – as transport mechanisms. When used in WLAN the protocol EAP will be referred to as EAPOL. The main 3GPP-WLAN interworking architecture is defined in 3GPP TS 23.234 [61]; the security architecture is found in 3GPP TS 33.234 [62].
A benefit of the loose interworking approach is that the 3GPP-WLAN architecture is a fairly simple architecture. The architecture contains the WLAN access network and a UMTS core network in addition to glue technology to connect the two systems. Figure 15.15 gives an overview of the proposed architecture [64]. The two key glue components of the interworking solution are the AAA and EAP technologies. These are used to execute the UMTS AKA protocol from the 3G system’s home domain toward the WLAN user equipment. The AAA architecture and the RADIUS and/or Diameter protocol are to be used as the bridge between the 3GPP system and the WLAN access network. Both Diameter and RADIUS are generic protocols and are intended to provide support for a diverse set of AAA applications, including network access, IP mobility and interoperator roaming. The EAP-AKA [67] protocol allows the UMTS AKA security protocol, which was originally

SECURITY IN AD HOC NETWORKS |
615 |
Home |
|
HSS |
|
||
|
|
|
|
|
|
environment– |
|
|
|
|
|
the home |
|
|
Wx |
||
network |
|
|
|
||
|
|
|
|
|
|
3GPP AAA
Wr |
3GPP AAA proxy
Serving |
|
network– |
Wr |
the visited |
|
network |
|
|
Internet/ |
WLAN |
NAS |
access |
intranet |
|
|
network |
AP |
|
UE
Figure 15.15 3GPP-WLAN architecture.
designed for execution over UTRAN, to be executed over the WLAN access toward the user equipment. EAP [63] is a key element in the 3GPP-WLAN security architecture. EAP provides, in essence, a generic peer-to-peer based request–response transaction environment for authentication dialogs, and supports multiple authentication mechanisms. EAP typically runs directly over the link layer without requiring IP. EAP has its own flow control mechanisms, and is capable of removing duplicate messages and retransmitting lost messages. EAP can be used over different link layer protocols including the IEEE WLAN link layer. The necessary EAP encapsulation is described in the EAP-over-LAN specification [68].
The EAP protocol does not natively provide much in terms of authentication mechanisms. Instead, its power lies in its generic mechanism to support existing authentication methods through specialized EAP methods. EAP contains a negotiation sequence where the authenticator requests information about which authentication method to use. The EAP architecture does not require the authenticator to support all authentication methods. Instead, the authenticator can request assistance from a backend authentication server to complete the authentication processing. The specific authentication methods supported are defined in separate specifications detailing how the EAP framework is to be used to run the target authentication methods. For 3GPPWLAN interworking, primary interest is in the EAP-AKA [64, 67] methods. An execution of the EAP-AKA procedure specific to the IEEE 802.11 WLAN is illustrated in Figure 15.16.
15.7 SECURITY IN AD HOC NETWORKS
Traditional security mechanisms, such as authentication protocols, digital signature and encryption, still play important roles in achieving confidentiality, integrity, authentication and nonrepudiation of communication in ad hoc networks. However, these mechanisms are not sufficient by themselves.

SECURITY IN AD HOC NETWORKS |
617 |
In the first case, nodes can protect routing information in the same way they protect data traffic, i.e. through the use of cryptographic schemes such as digital signature. However, this defense is ineffective against attacks from compromised servers. Worse yet, we cannot neglect the possibility of nodes being compromised in an ad hoc network. Detection of compromised nodes through routing information is also difficult in an ad hoc network because of its dynamically changing topology. When a piece of routing information is found to be invalid, the information could be generated by a compromised node, or, it could have become invalid as a result of topology changes. It is difficult to distinguish between the two cases.
On the other hand, certain properties of ad hoc networks can be exploited to achieve secure routing. For example, the routing protocols for ad hoc networks must handle outdated routing information to accommodate the dynamically changing topology. False routing information generated by compromised nodes could, to some extent, be considered outdated information. As long as there are sufficiently many correct nodes, the routing protocol should be able to find routes that go around these compromised nodes. Such capability of the routing protocols usually relies on the inherent redundancies due to multiple, possibly disjoint, routes between nodes in ad hoc networks. If routing protocols can discover multiple routes (e.g. protocols in ZRP, DSR, TORA and AODV, discussed in Chapter 13; all can achieve this), nodes can switch to an alternative route when the primary route appears to have failed.
Diversity coding, discussed in Chapter 7, takes advantage of multiple paths in an efficient way without message retransmission. The basic idea, discussed in Chapter 7, is to transmit redundant information through additional routes for error detection and correction. For example, if there are n disjoint routes between two nodes, then we can use n – r channels to transmit data and use the other r channels to transmit redundant information. Even if certain routes are compromised, the receiver may still be able to validate messages and to recover messages from errors using the redundant information from the additional r channels.
Key management service using a single CA (certification authority) in ad hoc networks is problematic. The CA, responsible for the security of the entire network, is a vulnerable point of the network. If the CA is unavailable, nodes cannot obtain the current public keys of other nodes or to establish secure communication with others. If the CA is compromised and leaks its private key to an adversary, the adversary can then sign any erroneous certificate using this private key to impersonate any node or to revoke any certificate.
A standard approach to improve availability of a service is replication. However, a simple replication of the CA makes the service more vulnerable. Compromise of any single replica, which possesses the service private key, could lead to collapse of the entire system. To solve this problem, the trust can be distributed to a set of nodes with a collective key management responsibility [69] .
In such a system, the service as a whole has a public/private key pair. All nodes in the system know the public key of the service and trust any certificates signed using the corresponding private key. Nodes, as clients, can submit query requests to get other clients’ public keys or submit update requests to change their own public keys.
The key management service, with an (n, t + 1) configuration (n ≥ 3t + 1), consists of n special nodes, called servers, located within an ad hoc network. Each server also has its own key pair and stores the public keys of all the nodes in the network. In particular, each server knows the public keys of other servers. Thus, servers can establish secure links among them. It is assumed that the adversary can compromise up to t servers in any period of time with a certain duration.
