
[ENG]_Rules
.pdf
ADVANCED COMBAT: HACKING
ADVANCED COMBAT: HACKING
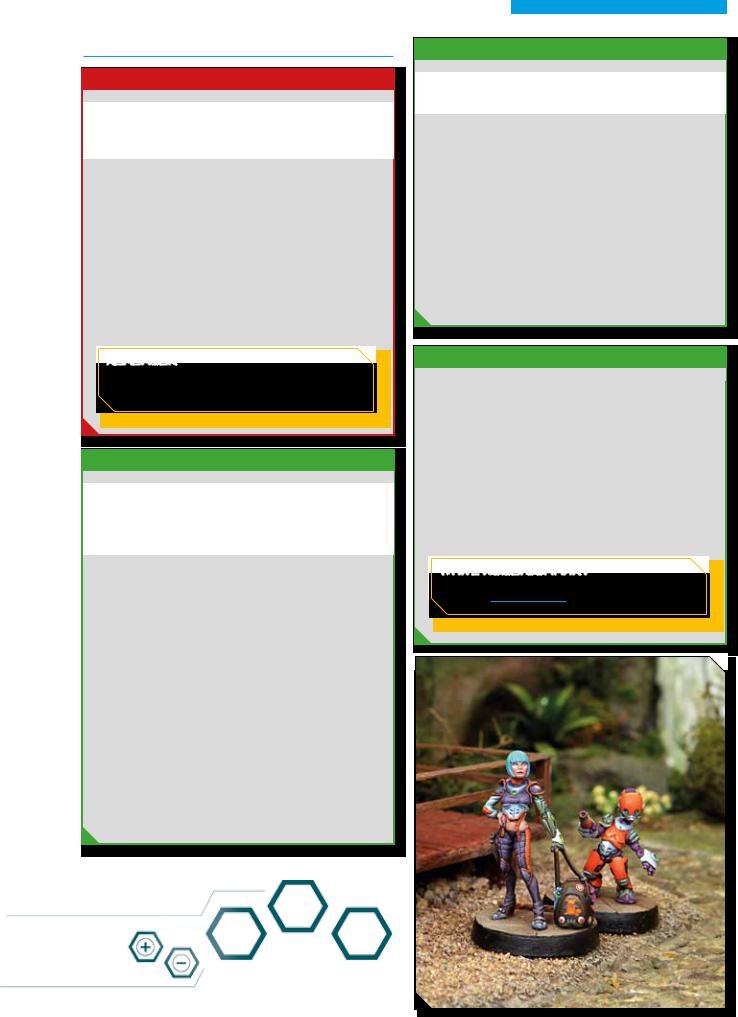
In a modern battlefield, computer and electronic systems are just as important as bombs and rifles,since they are the ones ensuring that everything works and moves in the right direction. Long distance communications are carried out with quantronic devices rather than by radio, which is now relegated to emergencysituations and mainlyused for short distance communications.Without proper communications, supplies and backup will never get anywhere, the artillery will never be able to take up a position, missiles will never be guided towards their targets,and troops will be unaware of the battlefield conditions and will not knowwhat theyare up against. A situation of general confusion reminiscent of the battlefields from the dawn of the twentieth century will take place. The only troops that can cause or prevent this kind of situation are theTactical Hackers: experts on infowar, cyberassaultandelectronicdefenseandcombat.Theyarethe troopers equipped and trained to use Hacking Devices in the maelstrom of the modern battlefield.
Hacking Devices are small quantronic computers, specially set up for infowar and cybercombat. They are used both to attackthe enemycomputer systems and as a defense against thesekindsofattacks.EachHackingDeviceusesspecificskills and hacking programs to fulfill a particular role in combat.
HACKING RULES
In the Infinityuniverse,cybercombat and infowar operations are collectively referred to as Hacking.Operatives equipped with a Hacking Device are called simply Hackers.
Hacking Devices comeinvariousmodelswithdifferentdegrees of specialization and Hacking Program suites.
Dependingontheirintendedpurpose,Hacking Programs allow their user to deployoffensive or defensive measures,support his allies,interact with his environment,etc.
Hackers mayonlyuse the Hacking Programs available to their
Hacking Device.
DABBLING IN
 HACKING
HACKING
Hacking rules are advanced rules.This doesn’t mean they arecomplexorconvoluted,buttheyareextensiveandcommitting them to memory in one sitting may be a daunting task.To ease you into the use of these advanced rules,we recommend an incremental approach.
Hacking worksverysimilarlyto other mechanics in Infinity, for example CCSpecial Skills.Start byreading the first few sections:TypesofHackingPrograms,HackingArea,Hacking Devices and Hacking Programs: Characteristics, Firewalls, and the legend to the Hacking Programs Table.
Next, choose the Hacking Device you intend to use (we recommend you try out a basic Hacking Device at least for the first few games) and check its entry in the quick reference table (page 250). Familiarize yourself with the programs available to you and how to use them. Hacking Programs are fairly straightforward. The info included in their table entryshould be enough to giveyou a good idea of what their purpose is,but you can find a more detailed explanation in the rules text for each individual program.
Once you feel comfortable assessing the merits of a given Hacking Device, compare them to find which model suits yourtacticalneedsbest.Withasolidgrasponthevirtuesof each available Hacking Device,you will be able to take full advantageoftheseadvancedrulesinnotime.Getconnected!
TYPES OF HACKING PROGRAMS
For ease of reference,Hacking Programs in Infinityare organized in a number of ways. They are primarily divided into a series of Types, according to their function and effect on the battlefield.
ThedifferentTypesofProgramarefurtherorganizedbyLevel. Access to one Level automaticallygrants theHacker access to all lower Levels of the same Type.
»»Control Programs (CLAW). Offensive programs designed to disable and stall enemy targets.
»»Attack Programs (SWORD). These programs are deployed withthespecificpurposeofincapacitatingenemyHackers.
»»Defensive Programs (SHIELD). These programs are used to defend from or neutralize the effects of enemyattacks.
»»Utility Programs (GADGET). A miscellaneous group of programs Hackers maydeployto affect their environment, their allies,or themselves.
»»Upgrade Programs (UPGRADE). Custom-made software tailoredtothestyleandpreferenceofspecificinfowarope- ratives.Theseprogramsaretoocomplexforstandard-issue Hacking Devices.
150




 NOISE: SUMMARY
NOISE: SUMMARY