
- •Contents
- •Preface
- •1 Introduction
- •1.1 Bluetooth system basics
- •1.1.1 Background
- •1.1.2 Trade-offs
- •1.1.3 Bluetooth protocol stack
- •1.1.4 Physical layer
- •1.1.5 Baseband
- •1.1.6 Link manager protocol
- •1.1.7 Logical link control and adaptation protocol
- •1.1.8 Host control interface
- •1.1.9 Profiles
- •1.2 Bluetooth security basics
- •1.2.1 User scenarios
- •1.2.2 Notions and terminology
- •References
- •2.1 Key types
- •2.2 Pairing and user interaction
- •2.3 Authentication
- •2.4 Link privacy
- •2.4.1 Protect the link
- •2.4.2 Encryption algorithm
- •2.4.3 Mode of operation
- •2.4.4 Unicast and broadcast
- •2.5 Communication security policies
- •2.5.1 Security modes
- •2.5.2 Security policy management
- •References
- •3 Bluetooth Pairing and Key Management
- •3.1 Pairing in Bluetooth
- •3.2 HCI protocol
- •3.3 LM protocol
- •3.4 Baseband events
- •3.4.1 Initialization key generation
- •3.4.2 Unit key generation
- •3.4.3 Combination key generation
- •3.4.4 Authentication
- •3.4.5 Master key generation
- •3.5 User interaction
- •3.6 Cipher key generation
- •3.7 Key databases
- •3.7.1 Unit keys generation requirements
- •3.7.2 Combination key generation requirements
- •3.7.3 Key databases
- •3.7.4 Semipermanent keys for temporary use
- •References
- •4 Algorithms
- •4.1 Crypto algorithm selection
- •4.1.1 Block ciphers
- •4.1.2 Stream ciphers
- •4.2 SAFER+
- •4.3 Encryption engine
- •4.4 Ciphering algorithm E0
- •4.4.1 Initialization
- •4.5 Implementation aspects
- •References
- •5 Broadcast Encryption
- •5.1 Overview
- •5.2 Preparing for broadcast encryption
- •5.3 Switching to broadcast encryption
- •References
- •6 Security Policies and Access Control
- •6.1 Objectives
- •6.1.1 Trust relations
- •6.1.2 Security levels
- •6.1.3 Flexibility
- •6.1.4 Implementation considerations
- •6.2 Security manager architecture
- •6.2.1 Overview
- •6.2.2 Device trust level
- •6.2.3 Security level for services
- •6.2.4 Connection setup
- •6.2.5 Database contents and registration procedure
- •Reference
- •7 Attacks, Strengths, and Weaknesses
- •7.1 Eavesdropping
- •7.2 Impersonation
- •7.3 Pairing
- •7.4 Improper key storage
- •7.4.1 Disclosure of keys
- •7.4.2 Tampering with keys
- •7.4.3 Denial of service
- •7.5 Unit key
- •7.6 Location tracking
- •7.6.1 Bluetooth device address and location tracking
- •7.6.2 Five different types of location tracking attacks
- •7.7 Implementation flaws
- •References
- •8 Providing Anonymity
- •8.1 Overview of the anonymity mode
- •8.2 Address usage
- •8.3 Modes of operation
- •8.4 Inquiry and paging
- •8.4.1 Connectable mode
- •8.4.2 Private connectable mode
- •8.4.3 General connectable mode
- •8.5 Alias authentication
- •8.6 Pairing
- •8.7 Anonymity mode LMP commands
- •8.8 Pairing example
- •References
- •9 Key Management Extensions
- •9.1 Improved pairing
- •9.1.1 Requirements on an improved pairing protocol
- •9.1.2 Improved pairing protocol
- •9.1.3 Implementation aspects and complexity
- •9.2 Higher layer key exchange
- •9.2.2 Higher layer key exchange with EAP TLS
- •9.3 Autonomous trust delegation
- •9.3.1 Security group extension method
- •9.3.3 Group extension method versus public key method
- •References
- •10 Security for Bluetooth Applications
- •10.1 Headset
- •10.1.1 Headset security model
- •10.1.2 Pass-key and key management
- •10.1.3 Example
- •10.2 Network access
- •10.2.1 Common access keys
- •10.2.2 Security architecture
- •10.2.3 Network service subscription
- •10.2.4 Initial connection
- •10.2.5 Subsequent access to NAcPs
- •10.3 SIM access
- •10.3.1 The SIM access profile
- •10.3.2 Securing SIM access
- •References
- •Glossary
- •List of Acronyms and Abbreviations
- •About the Authors
- •Index
136 |
Bluetooth Security |
The exchange of fixed addresses is only allowed to occur once encryption has been enabled for the connection to ensure that the anonymity is not compromised. Still, there is an anonymity risk with allowing usage of fixed addresses at all. However, this is the compromise that must be taken in order to have a reasonable trade-off between anonymity and user convenience requirements.
8.8 Pairing example
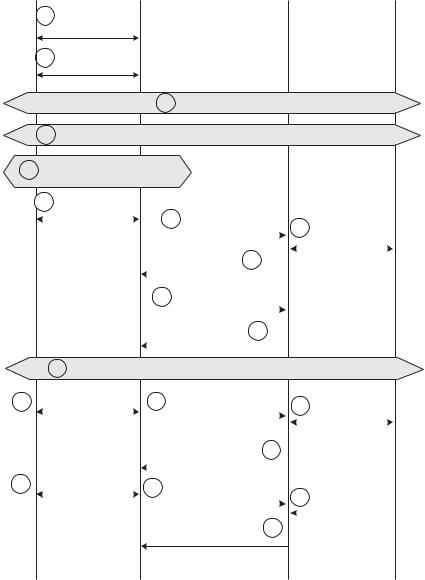
Finally, we give an example of how the presented anonymity modes work when two devices not previously known to each other connect and are paired with each other. We assume that the users of the devices have put their devices in private pairable mode and hence that the devices trust each other and will, in addition to creating a shared link key, exchange alias and private addresses. The main steps related to the connection and pairing procedure are illustrated in Figure 8.5. Below, we explain the procedure step by step.
1.The host that is hosting device A, sets the device in anonymous mode using a dedicated command.
2.Host A requires authentication and encryption for any devices that the host connects to or is connected with.
3.Device A searches for a new device using the Bluetooth inquiry procedure. A new Bluetooth device, here called device B, is discovered. Device A receives the active BD_ADDR_B from device B.
4.Device A pages device B using BD_ADDR_B.
5.During the connection setup, device A requires authentication. Since no link key is available, a manual pairing where the users enter a passkey must be performed.
6.Host A requests a pass-key from the user. The user enters the pass-key, which is transferred to the link manager through the HCI.
7.The link manager of device A sends a random number to the link manager of device B. The random number is used to calculate an initialization key.
8.The link manager of device B requests a pass-key from the user through the HCI. The user enters the pass-key, which is returned to the link manager.
9.The link manager of device B calculates the initialization key and return an accept LM PDU to device A.
Providing Anonymity |
137 |
|
|
Host A |
|
HC/LM-A |
|
HC/LM-B |
|
Host B |
|
master |
|
slave |
|
||
|
|
|
|
|
||
|
|
|
|
|
|
|
5
13
17
1Enable the anonymous mode
2Enable authentication and encryption
|
|
|
|
|
|
3 Inquiry |
|
|
|
|
|
|
|
||
4 |
Unit A pages on BD_ADDR_B and authentication is required |
|
|||||||||||||
No link key available |
|
|
|
|
|
|
|
|
|
|
|
||||
=> pass-key is required |
|
|
|
|
|
|
|
|
|
|
|||||
6 |
Pass-key request |
|
|
|
LMP in rand |
|
|
|
|
|
|
|
|||
|
and returned |
|
|
7 |
|
|
|
|
|
|
|
||||
|
|
|
|
|
|
|
(rand_nr) |
|
|
|
|
8 |
Pass-key |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||
|
|
|
|
|
|
LMP accepted |
|
|
|
|
|
requested |
|
||
|
|
|
|
|
|
9 |
|
|
|
and returned |
|
||||
|
|
|
|
|
|
(opcode) |
|
|
|
|
|||||
|
|
|
|
|
|
|
|
|
|
|
|||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
10 |
|
LMP comb key |
|
|
|
|
|
|
||
|
|
|
|
|
|
(rand nr) |
|
|
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
LMP_comb_key |
|
11 |
|
|
|
|
|
|||
|
|
|
|
|
(rand_nr) |
|
|
|
|
|
|
||||
|
|
|
|
|
|
||||||||||
|
12 |
Authentication and switching on encryption |
|
||||||||||||
Request for |
|
|
|
14 |
|
LMP fixed address |
|
Allow private |
|
||||||
exchange of fixed |
|
|
|
(BD_ADDR_FIXED_A) |
15 |
|
|||||||||
|
|
|
|
|
|
|
|
|
|
pairing? |
|
||||
|
|
|
|
|
|
|
|
|
|
|
|||||
addresses |
|
|
|
LMP fixed address |
|
16 |
|
|
|
|
|
||||
|
|
|
|
|
|
|
|
|
|||||||
|
|
|
|
|
|
|
|
|
|
|
|||||
|
|
|
|
|
(BD_ADDR_FIXED_B) |
|
|
|
|
|
|||||
Request for |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
LMP_alias_address |
|
|
|
||||||||
exchange of alias |
18 |
|
Request alias |
|
|||||||||||
(BD_ADDR_alias) |
|
|
|
19 |
|
||||||||||
addresses |
|
|
|
|
|
|
|
|
|||||||
|
|
|
|
|
|
LMP_alias_address 20 |
|
address |
|
||||||
|
|
|
|
|
|
|
|
|
|||||||
|
|
|
|
|
|
(BD_ADDR_alias) |
|
|
|
|
|
|
|
||
Figure 8.5 Message sequence for pairing with a trusted device.
10.Device A generates a random number that is used to calculate a combination key. The random number is sent encrypted with the initialization key to device B.
138 |
Bluetooth Security |
11.Device B receives the random number, generates its own random number, which is returned to device A encrypted with the initialization key. Both devices decrypt the received random values and calculate the secret combination key.
12.A mutual authentication is performed and the devices switch to encrypted mode.
13.Since device A is in private pairable mode, the host requests that a fixed address shall be exchanged.
14.The link manager of device A sends the fixed address, BD_ADDRfixed_A, to device B.
15.The link manager of device B receives the fixed address from A. Next, it asks the host if exchange of private information is allowed or not; that is, the host will tell whether or not device A is a trusted device that shall receive the fixed address. The host is in private pairable mode. Hence, it accepts fixed addresses to be exchanged.
16.The link manager of device B sends the fixed address, BD_ADDRfixed_B, to device B.
17.Next, the host of device A requests alias addresses to be exchanged and generates an alias that should be used when device B identifies device
A.
18.The link manager of device A sends the alias address,
BD_ADDR_alias_A, to device B.
19.Device B receives the alias address. The link manager sends the received alias address to the host through the HCI and asks the host for an alias to return. Either the host chooses to use the same alias (symmetric alias) or a different alias (asymmetric alias) is used.
20.The link manager of device B returns the alias address for device B,
BD_ADDR_alias_B, to device A.
References
[1]IEEE, IEEE Standard for Local and Metropolitan Area Networks: Overview and Architecture, IEEE Std. 802-2001, 2002.
[2]Bluetooth Special Interest Group, Specification of the Bluetooth System, Version 1.2, Core System Package, November 2003.
